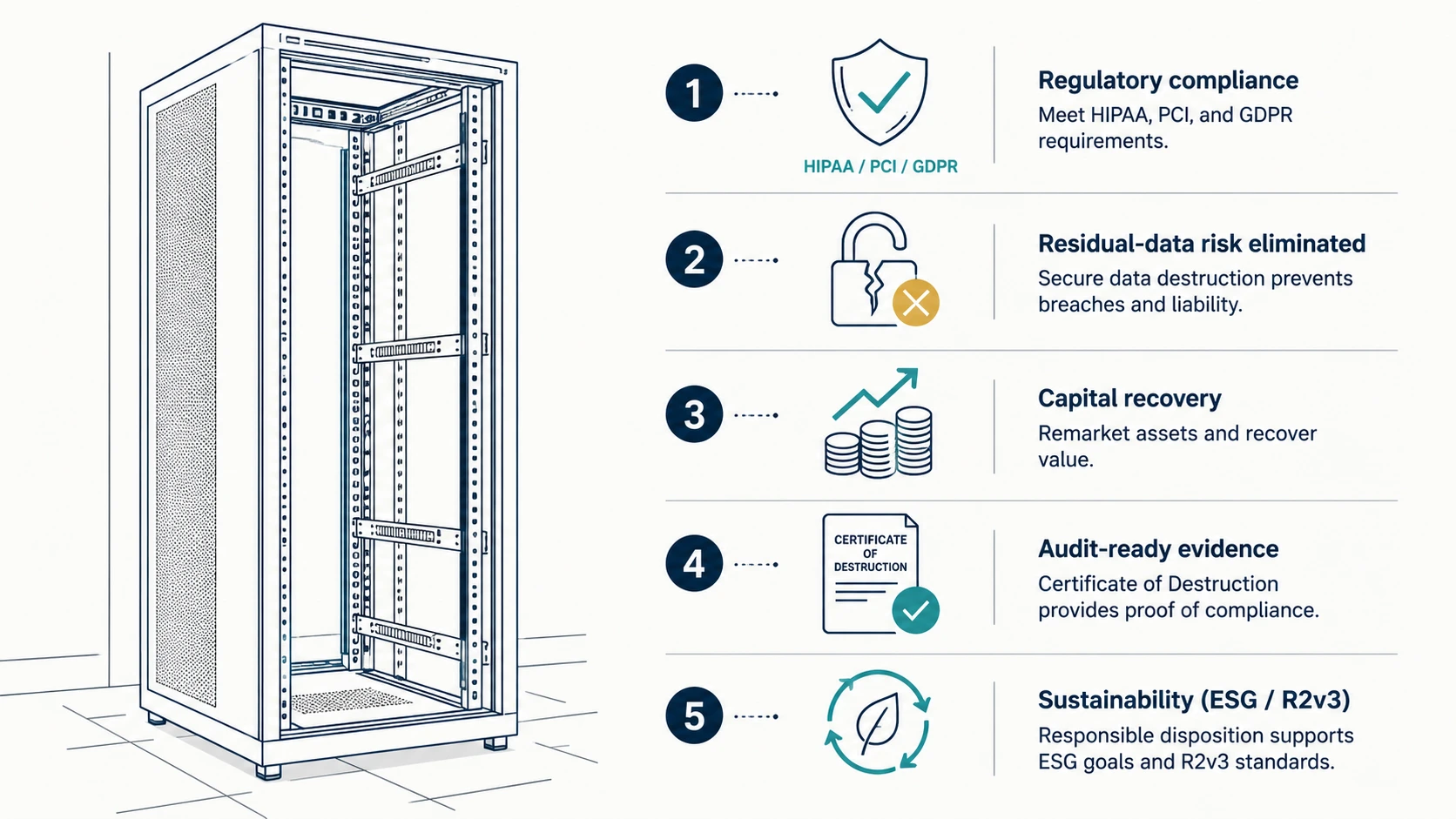
Data center decommissioning is the planned, documented retirement of compute, storage, networking, and supporting infrastructure from a facility that is being closed, consolidated, migrated, or refreshed. Done well, decommissioning produces audit-evidence artifacts that close the regulatory loop on every retired asset and recover residual capital from the asset stream. Done poorly, decommissioning leaves residual data on retired drives, leaves capital sitting in a chassis on a loading dock, and leaves the next regulator with an unsigned chain-of-custody log. This guide names the 5 reasons enterprise IT, finance, security, and compliance leaders fund a structured decommissioning engagement: regulatory compliance, residual-data breach risk, capital recovery, audit-evidence closure, and ESG alignment.
The audience is enterprise: CIO, IT decommissioning lead, CISO, CFO, and Compliance / GC. The reasons below are written for the people who fund and approve decommissioning, not the people who unbolt the racks.
What Is Enterprise Data Center Decommissioning?
Enterprise data center decommissioning is the structured retirement of an entire facility’s IT footprint: servers, storage arrays, networking gear, backup tape, optical media, and supporting infrastructure. It includes media sanitization to NIST SP 800-88 r1, chain-of-custody documentation, Certificate of Destruction issuance, and R2v3-aligned downstream recycling.
Decommissioning is not the same as a routine asset refresh. The defining traits of a decommissioning engagement are scale (hundreds to tens of thousands of assets), facility-level scope (the whole site, not a single rack), and a defined end-state (the building is empty, sold, returned to landlord, or repurposed). A decommissioning engagement runs as a project with a project plan, a security plan, a finance plan, and a closeout report.
The 5 reasons below explain why CIO, CFO, CISO, Compliance, and Decom Lead all sign off on the project. Each reason is anchored to a regulation, a financial control, a security framework, or a sustainability standard.
Reason 1: Regulatory Compliance Mandates Defensible Data Disposal
Every enterprise data category lives under a disposal regulation: HIPAA Disposal Rule for health, GLBA Safeguards Rule and FACTA Disposal Rule for financial, PCI DSS v4 Requirement 9.4 for cardholder data, FISMA / NIST 800-171 / CMMC 2.0 for federal, GDPR Article 17 for EU personal data, and state e-waste statutes for the asset itself.
A facility being decommissioned holds, on its drives, every category of data the organization processed there. If the decommissioning project does not document defensible disposal per the operative regulation for each data category, the next audit will produce a finding.
The most-cited disposal regulations the decommissioning project must satisfy:
- HIPAA Disposal Rule (45 CFR §164.310(d)(2)). Covered Entities and Business Associates must implement policies and procedures to address the final disposition of electronic protected health information and the hardware on which it is stored. The Office for Civil Rights enforcement record cites missing disposal documentation as a recurrent finding. NIST SP 800-66 r2 maps Section 164.310(d)(2) to NIST 800-88 r1 method selection. Decommissioning a data center that processes ePHI without producing a serial-numbered Certificate of Destruction is, in practice, an unmitigated finding.
- PCI DSS v4 Requirement 9.4. Cardholder data on electronic media must be rendered unrecoverable when no longer needed. The Payment Card Industry Security Standards Council names “destruction in such a way that data cannot be reconstructed” as the standard. Decommissioning that retires payment-environment infrastructure without method-aligned destruction and CoD evidence violates Requirement 9.4.
- GLBA Safeguards Rule and FACTA Disposal Rule. Financial-services Covered Entities must implement reasonable measures to dispose of customer information. The FTC enforces both. The Safeguards Rule (16 CFR Part 314) and the Disposal Rule (16 CFR Part 682) treat unmitigated disposal of customer information as an unfair-or-deceptive practice. Decommissioning a financial-services data center without a documented disposal program is enforcement-exposed.
- CMMC 2.0 and NIST 800-171 for defense contractors. Cleared and CUI-handling contractors must satisfy media-protection controls (MP-6 in NIST 800-53; 3.8 in NIST 800-171). Decommissioning a CUI-handling facility without on-site witnessed destruction or live-witness off-site destruction, with full chain-of-custody log, exposes the prime to a Defense Contract Management Agency or DCSA finding and downstream contract risk.
- GDPR Article 17 (right to erasure) and Article 32 (security of processing). EU personal data on retired media must be erased to a level that is irreversible. Article 32 obligations apply throughout the asset lifecycle, including disposal. EU Data Protection Authorities have issued enforcement actions against organizations that retired hardware without documented erasure.
- State e-waste statutes. Most states regulate the disposal of electronics-waste by class (covered electronic device, hazardous waste, etc.). California (Cal. Pub. Resources Code §42460), Texas (Tex. Health & Safety Code §361), New York, Illinois, Washington, and others impose recycler-certification, reporting, or generator-of-record obligations on the decommissioning enterprise.
Decommissioning closes the regulatory loop because every retired asset is documented to a defensible disposal method on a serial-numbered Certificate of Destruction. The CoD is the evidence artifact attached to the audit binder. Without the CoD, there is no defensibility record.
Reason 2: Decommissioning Eliminates Residual Data Breach Risk on Retired Assets
Retired assets that leave the facility without method-aligned media sanitization carry residual data into the disposal stream. The Verizon Data Breach Investigations Report and OCR HIPAA breach summaries record cases of breach-of-record events traced to drives sold at auction, donated to schools, or leased back to vendors with data intact.
The breach risk is not theoretical. Several patterns recur in published breach records:
- Resale-stream breaches. Drives sold to secondary-market buyers without sanitization. The buyer scans the drive, reconstructs the data, and either reports the breach or exploits it. The hospital, bank, or agency that retired the drive becomes the disclosing party under the operative breach-notification rule.
- Donation-stream breaches. Decommissioned servers donated to schools, nonprofits, or training programs without sanitization. The recipient has no obligation to protect the data; the data is effectively published.
- Lease-return breaches. Equipment returned to the leasing company at end of lease without contractually witnessed sanitization. The leasing company refurbishes and re-leases. Data follows the asset to the next leaseholder.
- Loading-dock breaches. Decommissioned media palletized on a loading dock awaiting a recycler, without sealed-container custody. Theft, photography, or interception during transit becomes the breach vector.
- Recycler-failure breaches. Media handed to an uncertified recycler that does not process drives to NIST 800-88 r1 standards. Drives recovered from the recycler’s downstream become the breach source.
A structured decommissioning project closes each of these vectors. Method-aligned media sanitization (Destroy for HDD and SSD, Purge or Destroy for tape, Destroy for paper, component-level destruction for equipment) followed by serial-numbered Certificate of Destruction issuance and R2v3 downstream recycling produces a complete audit-defensible disposal record. The retired asset cannot become a breach source because the asset is no longer recoverable.
The cost calculation is straightforward. The IBM Cost of a Data Breach Report places average breach cost in healthcare and financial services well above the cost of any decommissioning engagement. Avoiding one breach pays for many decommissioning projects.
Reason 3: Decommissioning Recovers Capital and Reduces Operational Cost
Decommissioning recovers capital across three streams: residual asset value (resale or component recovery), avoided operational cost (power, cooling, real estate, license), and recovered facility value (square footage returned to landlord or repurposed). Each stream has a measurable financial impact the CFO can model in the project business case.
The financial framing is the reason the CFO funds decommissioning even when compliance and security have already signed off.
- Residual asset value. Servers, storage arrays, and networking gear nearing end-of-life retain residual market value through certified ITAD vendors. The ITAD vendor sanitizes the asset to NIST 800-88 r1 Clear or Purge (where reuse is appropriate), refurbishes, tests, and resells. Net proceeds (after the vendor’s share) return to the customer. Component-level recovery (precious-metal reclamation from circuit boards, copper from cabling, aluminum from chassis) recovers additional value through R2v3-certified downstream processors.
- Avoided operational cost. Every rack-unit consumes power, cooling, and floor space. Industry power-cost benchmarks attribute typical enterprise rack-power consumption at multi-thousand-dollar annual cost per rack-unit, plus equivalent cooling. Decommissioning eliminates this run-cost. License-cost avoidance (server OS, hypervisor, monitoring, security agents) compounds the savings.
- Real estate recovery. Decommissioning a co-location footprint cancels the lease cost from the date the facility is signed back. Decommissioning an owned data center returns the square footage to the enterprise for repurpose (general office, lab, conference) or sale. Real estate recovery is often the single largest line item in the decommissioning business case.
- Avoided refresh cost. Decommissioning is typically paired with a migration to cloud, co-location, or a consolidated facility. Decommissioning prevents the temptation to refresh equipment that should not have been refreshed. The CFO captures the avoided capital expenditure as part of the decommissioning ROI.
The CFO funds decommissioning when the recovery streams above exceed the project cost. They typically do, by a substantial margin, on engagements with hundreds or thousands of assets. The vendor’s job is to model the recovery streams in the project proposal so the business case is defensible to the finance committee.
Reason 4: Decommissioning Closes the Audit-Evidence Loop with Chain of Custody and Certificate of Destruction
A retired asset is auditable until the moment it is destroyed and a serial-numbered Certificate of Destruction is issued. Decommissioning closes the audit-evidence loop by producing, per asset, a documented destruction record that ties the asset retirement list to the destruction record to the recycling stream.
Audit findings tied to retired assets are common because assets that leave the data center without proper documentation create a gap in the asset-tracking record. The auditor sees a serial number on the asset retirement list with no destruction record attached. The finding writes itself.
The audit-evidence chain produced by a properly run decommissioning engagement:
- Asset retirement list. A spreadsheet or asset-management-system export naming every retired asset by serial number, model, location, and data category. The decommissioning project starts with this list.
- Sealed-container intake manifest. At intake, every asset is logged into a sealed container with a manifest naming the container ID, the asset count, the serial-number list, and the custodian signatures (customer and vendor).
- Chain-of-custody log. At every transfer (intake, transport, staging, destruction, recycling-stream handoff), the manifest is signed and timestamped. GPS or routed-truck verification documents the transport leg.
- Destruction record. At destruction, the technician (and witness, where applicable) records the method, achieved particle size, destruction date and time, destruction location, and asset count.
- Certificate of Destruction. Within 5 business days of destruction, the vendor issues a serial-numbered Certificate of Destruction naming the customer entity, destruction date and location, method, achieved particle size, technician and witness, asset serial numbers (one per row), regulatory reference, and recycling stream reference.
- Recycling-stream record. The R2v3 or e-Stewards downstream processor receives the post-destruction commodity stream and records the receipt. The vendor retains the recycling-stream record alongside the CoD.
- Closeout report. The vendor produces a project closeout report mapping every line on the asset retirement list to a CoD line. Reconciliation is 1:1 by serial number. Variances are explained.
The closeout report is the audit-defensibility artifact the customer attaches to the audit binder. The OCR HIPAA reviewer, the FTC Safeguards Rule investigator, the DCSA inspector, and the SOX-controls examiner ask the same question: “Show me the disposal record for this asset.” The closeout report answers it on demand.
Reason 5: Decommissioning Aligns ITAD with ESG and R2v3 Reporting Obligations
Decommissioning aligned to R2v3 or e-Stewards downstream certification produces the data the enterprise reports under SEC climate disclosures (where applicable), CDP, GRI, SASB, and internal sustainability dashboards. ESG reporting expects evidence of certified-recycler downstream and CO2-equivalent reduction from refurbishment-over-replacement.
The ESG framing matters because the audience for the decommissioning business case has expanded. Where the CIO and CFO once led the decision, the Chief Sustainability Officer now reviews the project for ESG impact. Decommissioning that lands in landfill, exports to non-OECD jurisdictions, or moves through uncertified recyclers exposes the enterprise to ESG-disclosure scrutiny and investor questioning.
- R2v3 certified-recycler downstream. R2v3, administered by Sustainable Electronics Recycling International, requires the certified recycler to track downstream processors through to final disposition. The decommissioning project that uses R2v3 vendors produces the disposition record needed for ESG disclosure.
- e-Stewards alternative. e-Stewards, administered by the Basel Action Network, applies stricter export controls on non-OECD shipments. Some enterprises prefer e-Stewards for the export-control posture; either certification satisfies most ESG reporting frameworks.
- Refurbishment-over-replacement reporting. Decommissioning that returns asset components to the secondary market through certified ITAD vendors documents reuse mass and avoided-replacement carbon. The carbon-equivalent calculation feeds CDP and SBTi reporting.
- Hazardous-material handling. Some retired equipment contains lead, mercury, or cadmium under EPA Universal Waste Rule or state hazardous-waste rule. R2v3 and e-Stewards certified processors document the handling stream. The decommissioning customer is the generator of record under most state rules; the certified-recycler downstream is the documentation chain.
- Landfill diversion reporting. Many enterprises report “zero-landfill” goals on retired electronics. Decommissioning through R2v3 or e-Stewards is the operational mechanism by which the goal is achieved.
The decommissioning project produces, alongside the Certificate of Destruction package, an ESG impact summary the Chief Sustainability Officer can attach to annual reporting. The summary names the certified-recycler downstream, mass diverted from landfill, refurbishment-rate, and CO2-equivalent reduction.
When Should the Enterprise Schedule Data Center Decommissioning?
Schedule decommissioning when one of five triggers fires: facility closure or consolidation, cloud or co-location migration, a refresh cycle that retires the legacy footprint, a merger or acquisition that produces redundant facilities, or a compliance event that mandates documented disposal. Each trigger has a different timeline; none is “whenever convenient.”
| Trigger | Typical Timeline | Critical Path |
|---|---|---|
| Facility closure or consolidation | 6 to 18 months | Lease termination date drives the deadline; under-running the timeline generates rush charges and increased risk |
| Cloud or co-location migration | 12 to 36 months | Decommissioning starts after migration cutover and runs in parallel with cutover for hardware no longer in use |
| Refresh cycle | 3 to 9 months | Retiring legacy gear as new gear arrives; the refresh budget often funds the decommissioning |
| M&A integration | 6 to 24 months post-close | Day-1 inventory reveals redundant facilities; integration plan schedules decommissioning of the redundant footprint |
| Compliance event | Per consent decree or remediation plan | Regulator-imposed timeline; cannot be missed; vendor selection must happen on accelerated schedule |
Procurement and the Decom Lead should select the decommissioning vendor 90 to 180 days before the destruction work begins, to allow time for the Master Service Agreement, Statement of Work, security review, and asset-list reconciliation.
What Does an Enterprise Data Center Decommissioning Engagement Include?
A complete engagement includes asset inventory and reconciliation, sealed-container intake, transport with chain-of-custody log, media sanitization to NIST 800-88 r1 method per media type, witness mode per the SOW, Certificate of Destruction issuance, R2v3 downstream recycling, residual-value recovery (where applicable), and a project closeout report.
Decommissioning is more than physical destruction. The engagement is project-managed end to end. The vendor’s deliverables across the engagement, in typical sequence:
- Project plan with milestones, security plan, and SOW
- Asset-list reconciliation against customer asset-management system
- Risk assessment per data category and per regulation
- Sealed-container intake at customer site, with manifest signed by customer custodian and vendor custodian
- Chain-of-custody log at every transfer, GPS or routed-truck verification on transport
- Witness mode per SOW (on-site, live-video, or off-site sealed-container)
- Method-aligned media destruction per NIST 800-88 r1 per media type
- Certificate of Destruction within 5 business days of destruction
- Residual-value recovery for assets where reuse is approved (NIST 800-88 r1 Clear or Purge, refurbishment, resale)
- R2v3 or e-Stewards downstream recycling for non-reuse commodity stream
- ESG impact summary covering mass diverted, certified-recycler downstream, CO2-equivalent reduction
- Project closeout report mapping asset list to CoD, with variances explained
A vendor that does not produce all 12 deliverables on a decommissioning engagement is providing partial service. The customer becomes responsible for the gap, and the gap is where the audit finding lives.
Frequently Asked Questions
Is data center decommissioning the same as IT asset disposition (ITAD)?
Decommissioning is a project-scoped engagement that retires an entire facility or major footprint; ITAD is the ongoing service that processes routinely retired assets. Decommissioning typically includes ITAD as a sub-discipline. Most enterprises run a recurring ITAD program and engage decommissioning specialists for facility-level events.
Should the enterprise destroy every drive or refurbish some for resale?
The answer is per data category and per regulation. Drives that processed regulated data (HIPAA, GLBA, PCI, defense CUI) typically require Destroy under NIST 800-88 r1. Drives outside regulated scope can be Cleared or Purged for refurbishment when the residual-value calculation supports resale. The decision is made line-by-line on the asset list, not at the program level.
How long does a complete data center decommissioning take?
A small-to-medium engagement (a few hundred assets in a co-location footprint) runs 4 to 12 weeks. A large engagement (full owned data center, thousands of assets, multiple sites) runs 6 to 18 months. The critical path is asset reconciliation, security review, and lease-termination or migration cutover dependencies, not destruction throughput.
Who signs the Certificate of Destruction and the closeout report?
The vendor’s NAID AAA-certified technician (and witness, where applicable) signs each Certificate of Destruction. The vendor’s project manager signs the closeout report. The customer typically counter-signs the closeout report on receipt and attaches it to the audit binder for the regulatory retention period.
What insurance limits should the decommissioning vendor carry?
Typical floor for an enterprise decommissioning engagement is $5,000,000 general-liability per occurrence and $10,000,000 cyber-incident-liability aggregate. Engagements involving classified media, large patient-record volumes, or financial-services cardholder data warrant higher limits. Procurement should require certificates of insurance with the proposal.
Can decommissioning be done remotely with a video witness, or does the customer need to be on site?
Live-video witnessed off-site destruction is acceptable for many engagements, including most commercial enterprise scope. On-site witnessed destruction with a NAID AAA mobile shredding truck is the higher-assurance option and is typical for cleared-defense, federal high-side, and high-sensitivity commercial engagements. The Statement of Work names the witness mode per engagement.
Which Related Resources Cover Data Center Decommissioning Evidence and Method in Depth?
Enterprise IT, finance, security, and compliance leaders planning a decommissioning engagement typically pair this guide with the regulatory references and service-mode references that cover the specifics named above: HIPAA disposal documentation, PCI DSS v4 cardholder-data destruction, on-site witnessed shredding mechanics, supply-chain ITAD vendor vetting, and the broader data destruction service overview.
For the regulatory citations applied above, review Data Destruction Inc.’s HIPAA data destruction requirements and PCI DSS data destruction requirements, which break down 45 CFR §164.310(d)(2) and PCI DSS v4 Requirement 9.4 with the audit-evidence specifics the decommissioning closeout report should produce. For the editorial framework on vendor vetting at decommissioning scale, Data Destruction Inc.’s supply-chain data sanitization vendor vetting covers ITAD-vendor due diligence beyond NAID AAA. For the operational mechanics of on-site mobile shredding during a facility decommissioning, see hard drive shredding and the underlying data destruction service overview. CIOs and Decom Leads scoping a project can request a decommissioning engagement plan and CoD format sample by phone at (866) 850-7977 or through the contact form.
