Selecting a hard drive destruction vendor is a defensible-decision exercise: Procurement and the CISO must produce, on audit demand, evidence that the vendor’s methods, certifications, and chain of custody align with NIST SP 800-88 r1, NAID AAA Certification Standards, and the regulatory regime governing the data category. This guide names the 9 evaluation criteria CISOs use, the standards each criterion is anchored to, and the exact RFP language Procurement should require.
The audience is enterprise: federal agencies, defense contractors, large hospitals, large banks, F500 IT, and data center operators. The advice does not apply to consumer or small-office disposal of a single drive.
Why Is Vendor Selection for Hard Drive Destruction a Compliance-Cited Decision?
Hard drive destruction vendor selection is a compliance-cited decision because every method, certification, witness mode, and Certificate of Destruction issued must map back to a recognized standard the auditor or regulator can verify against NIST SP 800-88 r1, NAID AAA, and the operative regulation.
Procurement officers and CISOs cannot defend a vendor choice on price or convenience alone. The Office for Civil Rights (OCR) HIPAA enforcement record, FTC Safeguards Rule actions, and DCSA inspection findings consistently turn on documentary evidence: which method was used, who witnessed it, what particle size was achieved, and whether the Certificate of Destruction names the serial numbers and the operative standard.
The default federal media-sanitization standard is NIST SP 800-88 r1, published December 2014. It defines 3 sanitization categories (Clear, Purge, Destroy) and prescribes method selection by media type, security category, and reuse intent. DoD 5220.22-M, often cited in legacy procurement language, has been superseded for federal scope by NIST 800-88; pages and policies that name DoD 5220.22-M as the primary standard should be updated to reference NIST 800-88 with DoD as legacy compatibility.
The procurement decision turns on whether the vendor can produce evidence that satisfies the auditor or regulator who reviews the engagement after the fact, not on whether the vendor’s website looks polished.
What Are the 9 Criteria for Choosing a Hard Drive Destruction Company?
The 9 criteria are: NAID AAA certification, NIST 800-88 r1 method alignment, R2v3 or e-Stewards downstream recycling certification, ISO 27001 information security management, employee background-check standard, insurance and bonding limits, witness-mode availability, Certificate of Destruction format, and chain-of-custody documentation.
Each criterion is named below with the standard it maps to and the procurement-defensible reason to require it.
- NAID AAA Certification (current revision): NAID AAA is the recognized industry certification administered by i-SIGMA for secure data destruction service providers. Audited annually by independent third parties, it covers operational, employee, and physical-security requirements. Require a current certificate of compliance attached to the RFP response.
- NIST SP 800-88 r1 method alignment: The vendor must declare which NIST 800-88 category each service satisfies (Clear / Purge / Destroy) and document the mapping in writing. For hard drive shredding, the answer is Destroy, achieved at NIST-acceptable particle size.
- R2v3 or e-Stewards downstream recycling: Sustainable Electronics Recycling International administers R2v3; the Basel Action Network administers e-Stewards. Either certification confirms that post-destruction remnants enter a chain of certified downstream processors that meet international export and environmental controls.
- ISO/IEC 27001 information security management: ISO 27001 certification demonstrates that the vendor operates an information-security management system audited against international consensus controls. Pair with ISO/IEC 27040 alignment for storage-security specifics.
- Employee background-check standard: At minimum, NAID AAA-equivalent employee vetting (criminal history, drug screening, ongoing periodic re-checks). For cleared (defense) work, require U.S. Government Personnel Security Clearance equivalence at the level of the data being handled.
- Insurance and bonding: Require the vendor’s general-liability and cyber-incident liability policy limits in writing. Typical floor for enterprise engagements: $5M general liability, $10M cyber-incident coverage. Bonding evidences financial backing in the event of loss-in-transit claims.
- Witness-mode availability: On-site witnessed, live-video witnessed, and customer-personnel direct observation are the three modes the buyer can require. The RFP must name which mode is required and the vendor must confirm capability.
- Certificate of Destruction format: The CoD must list, at minimum: customer name, destruction date and location, technician name, witness name (where applicable), method, achieved particle size, drive serial numbers (one per row), regulatory reference, and a unique serial number for the certificate itself. NAID AAA reporting requirements are the minimum baseline; the customer’s regulator may demand more.
- Chain-of-custody documentation: Sealed-container manifest at intake, signed transfer at every custody change, GPS or routed-truck verification for transport, locked staging at the destruction facility, and timestamped destruction record. Each step must be evidenced and retained for the customer’s regulatory retention period.
The vendor that cannot produce documentation against all 9 criteria is, by definition, not the right vendor for an enterprise engagement.
Which Standards and Certifications Should the Vendor Hold?
The vendor must hold NAID AAA Certification, declare alignment with NIST SP 800-88 r1, hold R2v3 or e-Stewards for downstream recycling, and ideally hold ISO/IEC 27001. Defense engagements add NISPOM 32 CFR §117 and a relevant facility security clearance.
The certification stack matters because each certification covers a different domain of vendor risk:
| Certification / Standard | Covers | Issued / Maintained By | Relevance |
|---|---|---|---|
| NAID AAA | Secure-data-destruction operations, employee vetting, audit cadence | i-SIGMA | Required floor for enterprise engagements |
| NIST SP 800-88 r1 | Method selection, sanitization category mapping | NIST (federal guideline) | Governs technical method validity |
| R2v3 | Downstream electronics recycling controls | SERI | Required when recycling stream matters (most enterprise) |
| e-Stewards | Downstream recycling controls (alternative to R2v3) | Basel Action Network | Stricter on certain export rules |
| ISO/IEC 27001 | Information-security management system | National accreditation bodies | Demonstrates operational maturity |
| ISO/IEC 27040 | Storage-security specifics | International standard | Aligns with NIST 800-88 in international engagements |
| ISO 14001 | Environmental management | National accreditation bodies | Environmental side of the recycling stream |
| NISPOM 32 CFR §117 | Cleared-defense facility-security requirements | DCSA | Required for cleared-defense engagements |
Vendors that cite “ISO certified” without naming the standard, or “NIST compliant” without naming the revision, fail the citation-precision bar. Procurement should reject responses that lack specific standard names, revisions, and effective dates.
How Should the Vendor Document Chain of Custody and Witness Modes?
Chain of custody must be documented at every transfer point: intake, transport, staging, destruction, and recycling-stream handoff. Each transfer carries a signed, timestamped manifest naming the custodian, the asset count, and the asset serial numbers. Witness modes are named per engagement in the SOW.
Three witness modes are recognized:
- On-site witnessed destruction: A vendor mobile shredding truck arrives at the customer’s facility. The customer’s designated witness verifies media intake by serial number and observes the destruction in real time. Evidence: signed manifest, timestamped video (optional but preferred), Certificate of Destruction issued same-day.
- Live-video witnessed destruction: Off-site destruction with the customer’s witness observing via secure live video stream. Evidence: video recording, signed manifest, Certificate of Destruction with video reference.
- Off-site destruction without live witness: Sealed-container intake at customer site, GPS-tracked transport, locked staging, destruction at vendor facility. Evidence: chain-of-custody log, photographic record of destruction, Certificate of Destruction.
The buyer chooses the witness mode based on regulatory exposure and internal policy. Defense (cleared) and federal high-side engagements typically require on-site witnessed destruction; commercial enterprise engagements often accept off-site with sealed-container custody when the vendor’s NAID AAA certification and CoD format are sufficient for the auditor.
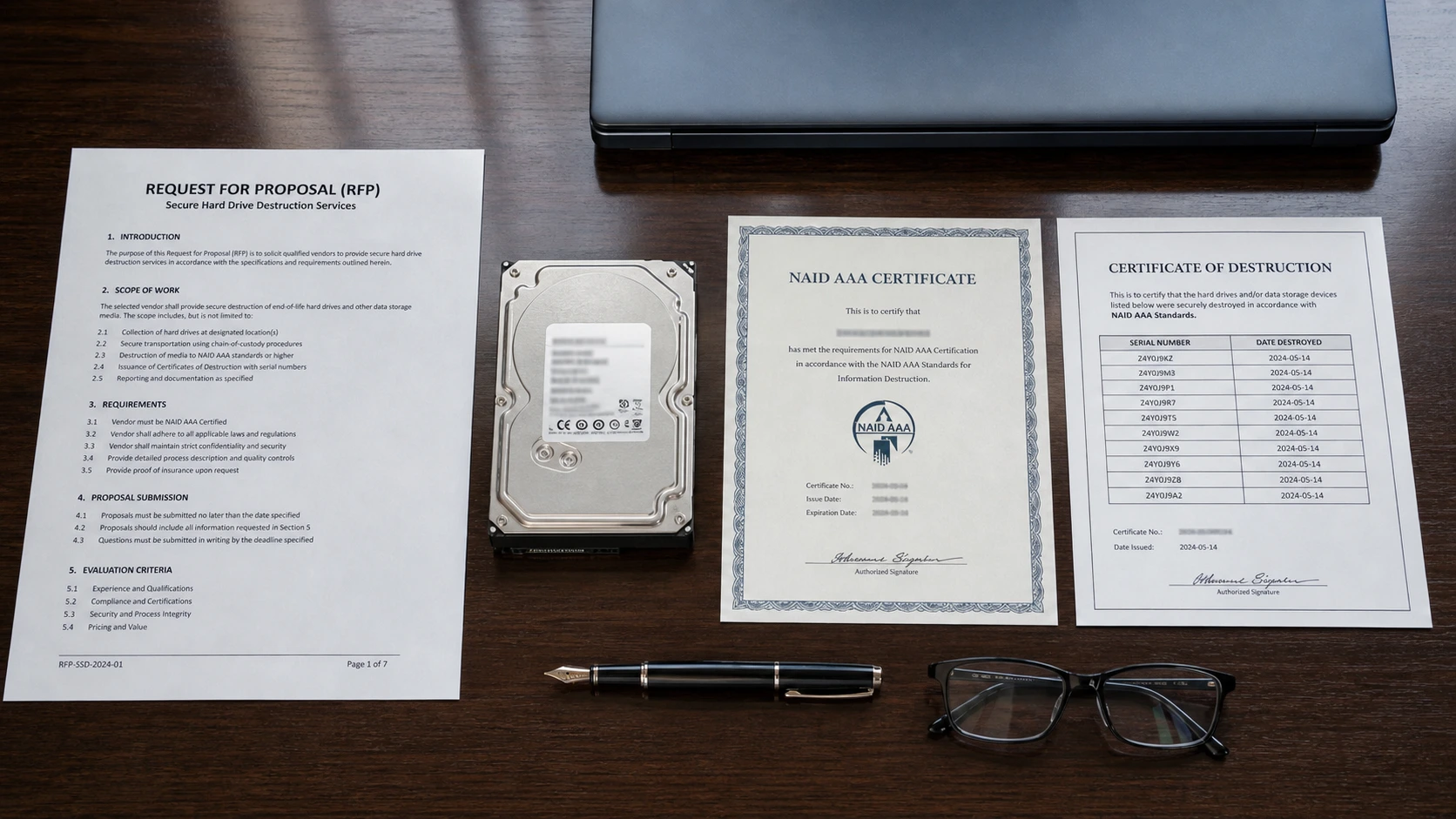
What Should the Certificate of Destruction Contain?
A defensible Certificate of Destruction names the customer, destruction date and location, method, achieved particle size, technician and witness, drive serial numbers (one per row), regulatory reference, and a unique CoD serial number. NAID AAA reporting requirements are the minimum baseline.
The CoD is the audit-evidence artifact that the customer attaches to the audit binder, the OCR HIPAA evidence packet, the DCSA inspection response, or the FTC Safeguards Rule documentation. A CoD missing serial numbers, missing the operative standard reference, or missing the witness name (when witnessed) is, in practice, indefensible.
A defensible CoD includes the following fields. Procurement should require this field list as a contract attachment.
- Customer name and address (the legal entity, not a brand)
- Data Destruction Inc. engagement / job number (vendor-internal)
- Unique CoD serial number
- Destruction date and time (timestamped)
- Destruction location (facility address or on-site customer address)
- Method (e.g., shredding, pulverization, degaussing)
- Achieved particle size (e.g., ≤ 6–10 mm for commercial; ≤ 2 mm for NSA-listed disintegrator)
- Technician full name, signature, and certification reference
- Witness full name and signature (when applicable)
- Drive serial number list (one row per drive)
- Asset count and weight (verification cross-check)
- Regulatory reference (e.g., NIST SP 800-88 r1 Destroy; HIPAA 45 CFR §164.310(d)(2))
- Recycling stream reference (R2v3 or e-Stewards downstream processor)
- Vendor NAID AAA seal and certificate number
The CoD is delivered within 5 business days of destruction (Data Destruction Inc. standard) and retained by the customer for the regulatory retention period applicable to the data category (e.g., 6 years from the date of creation or last effective date for HIPAA documentation per 45 CFR §164.530(j)(2)).
How Do On-Site and Off-Site Hard Drive Destruction Service Modes Compare?
On-site destruction sends a NAID AAA mobile shredding truck to the customer’s facility, with destruction witnessed live by customer personnel. Off-site destruction uses sealed-container intake, GPS-tracked transport, and destruction at the vendor’s facility. Each satisfies NIST 800-88 Destroy when correctly executed.
The two modes differ on witness availability, throughput, scheduling, and per-drive cost. The choice is procurement-driven, not technical-method-driven.
| Attribute | On-Site | Off-Site |
|---|---|---|
| Witness mode | Live, in-person | Sealed-container custody; live-video optional |
| Destruction location | Customer facility | Vendor facility |
| Throughput | 1,000–1,500 drives / hour (truck-mounted shredder) | Higher (industrial fixed plant) |
| Scheduling | Truck dispatch (lead time required) | Flexible (sealed-container pickup) |
| Per-drive cost | Higher (truck mobilization) | Lower |
| Audit defensibility (NIST 800-88) | High; on-site witness produces strongest evidence | High when sealed-container custody and CoD are correct |
| Best for | Federal high-side, defense (cleared), HIPAA Covered Entities under audit | Commercial enterprise, recurring decommissioning programs |
Both modes are recognized by NIST SP 800-88 r1 when the achieved particle size and chain-of-custody documentation meet the standard. The choice is a procurement and risk-tolerance call.
What RFP Language Should Procurement Require?
Procurement should require the vendor to attest, in writing, to NAID AAA certification, NIST 800-88 r1 method alignment per service, witness-mode capability, CoD field list, chain-of-custody documentation, insurance and bonding floors, and downstream recycling certification. The 8 RFP clauses below are minimum copy-paste language.
The following clauses are minimum RFP language. Procurement should adapt them to the engagement scope and add regulator-specific clauses (e.g., HIPAA Business Associate Agreement, DFARS 252.204-7012 for defense).
- Certification attestation. “Vendor shall be NAID AAA Certified at the time of contract award and for the full term of the engagement. A current Certificate of Compliance shall be attached to the response and re-attached annually.”
- Standard alignment. “Vendor shall declare, per service, the NIST SP 800-88 r1 sanitization category satisfied (Clear, Purge, or Destroy) and the achieved technical specification (e.g., particle size for physical destruction, overwrite passes for Clear, key-destruction verification for cryptographic erase).”
- Witness mode. “Vendor shall provide on-site witnessed destruction with mobile shredding truck on customer premises, OR off-site sealed-container destruction with live-video witnessing available at customer election. Vendor shall confirm capability for both modes in the response.”
- Certificate of Destruction. “Vendor shall issue a Certificate of Destruction within 5 business days of every destruction batch. The CoD shall name customer entity, destruction date and location, method, achieved particle size, technician and witness, drive serial numbers (one per row), unique CoD serial number, regulatory reference, and downstream recycling stream reference.”
- Chain of custody. “Vendor shall document chain of custody at every transfer with timestamped, signed manifest naming custodian, asset count, and asset serial numbers. Vendor shall retain chain-of-custody documentation for 7 years and provide on customer request.”
- Insurance and bonding. “Vendor shall maintain general-liability insurance not less than $5,000,000 per occurrence and cyber-incident liability not less than $10,000,000 aggregate. Vendor shall provide certificates of insurance with the response and update annually.”
- Downstream recycling. “Vendor shall use only R2v3-certified or e-Stewards-certified downstream processors for post-destruction recyclables. Vendor shall name the downstream processor(s) in the response and notify customer of any change during the engagement.”
- Regulatory alignment. “Vendor shall identify the regulations applicable to the data category covered by this engagement (HIPAA, GLBA, FACTA, SOX, PCI DSS v4, CMMC 2.0, FISMA / NIST 800-171, GDPR, state e-waste statutes) and confirm method and CoD alignment with each.”
A vendor that cannot return language-compliant responses to clauses 1–8 is not credentialed for the engagement.
What Common Mistakes Should Procurement Avoid When Selecting a Hard Drive Destruction Company?
The 5 most common mistakes are: accepting NIST 800-88 verbal claims without revision and category specifics, accepting DoD 5220.22-M as the primary federal standard, accepting Certificates of Destruction without serial-number lists, accepting off-site destruction without sealed-container custody, and selecting on price alone without certification and insurance verification.
These anti-patterns recur across enterprise procurement audits.
- Accepting “NIST compliant” without revision and category. NIST SP 800-88 has multiple revisions (the current is r1). Compliance is per-method-per-category. A vendor saying “NIST compliant” without specifying r1 and naming the category (Clear / Purge / Destroy) is making a non-citation. Reject the response.
- Accepting DoD 5220.22-M as the primary federal standard. DoD 5220.22-M is the legacy 3-pass overwrite specification. NIST SP 800-88 supersedes it for federal scope. Vendors leading with DoD 5220.22-M are signaling outdated practice. Require NIST 800-88 r1 as primary; accept DoD 5220.22-M as legacy compatibility only.
- Accepting CoDs without drive serial numbers. A CoD without serial numbers cannot be tied to specific assets. The auditor cannot verify that the destroyed drives match the customer’s asset retirement list. Require the serial-number list as a non-negotiable CoD field.
- Accepting off-site destruction without sealed-container custody. Off-site is acceptable when the chain of custody is documented from sealed-container intake at customer site through destruction. Off-site destruction with unmanned drop-off and no signed manifest at every transfer is not defensible.
- Selecting on price alone. The lowest bid is not the most defensible bid. The defensibility test is whether the vendor’s documentation will withstand an OCR HIPAA review, a DCSA inspection, an FTC Safeguards Rule investigation, or a SEC SOX-controls examination. Price competitiveness matters, but only among vendors that pass the certification and documentation bar.
Which Vendor Type Should You Choose?
Choose by engagement scope, regulatory exposure, and witness requirement. The matrix below names the recommended vendor profile for the most common enterprise scenarios. The decision is the buyer’s; the criteria are the same.
- For federal high-side or defense (cleared) engagements, choose a NAID AAA-certified vendor with a cleared facility under DCSA inspection and on-site witnessed destruction capability. Live-witness and CoD with classification reference are mandatory.
- For HIPAA Covered Entities and Business Associates, choose a NAID AAA-certified vendor with explicit BAA willingness, on-site witnessed destruction option, and CoD that names the HIPAA Disposal Rule citation. Off-site with sealed-container custody is acceptable when the auditor accepts.
- For PCI DSS v4 environments (Requirement 9.4), choose a NAID AAA-certified vendor whose CoD references PCI DSS v4 9.4 and whose method maps to NIST 800-88 Destroy for cardholder-data media.
- For data center decommissioning at scale, choose a vendor with industrial off-site capacity (high throughput), R2v3 downstream, and recurring-engagement scheduling. On-site truck for witnessed destruction can be added for the high-sensitivity subset.
- For state-level public-sector engagements, choose a NAID AAA-certified vendor that names the operative state statute (e.g., Cal. Civ. Code §1798.81.5; Tex. Bus. & Com. Code §521) and the federal interaction (HIPAA / GLBA / FACTA where applicable) in the SOW.
- For mixed-media decommissioning (HDD plus SSD plus tape), choose a vendor whose method-to-media mapping is explicit per NIST 800-88 r1: shredding for HDD, shredding to ≤ 2 mm with optional cryptographic erase for SED-SSDs, degaussing or shredding for tape, with one Certificate of Destruction covering the batch.
The wrong vendor is one who answers “yes to everything” without the citations or the documentation. The right vendor names the standard, the revision, and the evidence artifact.
Frequently Asked Questions
Is NAID AAA Certification a regulatory requirement or an industry baseline?
NAID AAA Certification is an industry-administered third-party-audited standard, not a federal regulation. However, the OCR HIPAA enforcement record, FTC Safeguards Rule findings, and DCSA inspection guidance all treat NAID AAA as the de facto floor for defensible vendor selection. Enterprise Procurement should require it.
Does NIST SP 800-88 r1 require physical destruction of every hard drive?
NIST SP 800-88 r1 does not mandate physical destruction. Section 5.1 of the publication permits Clear, Purge, or Destroy depending on the data’s security category and reuse intent. Most enterprise media leaving the data center receive Destroy treatment because reuse risk is unacceptable.
Is DoD 5220.22-M still acceptable as a destruction standard?
DoD 5220.22-M remains acceptable as a legacy reference but is superseded for federal scope by NIST SP 800-88 r1. Procurement language should name NIST 800-88 r1 as primary and DoD 5220.22-M as legacy compatibility only. Vendors leading with DoD 5220.22-M are signaling outdated practice.
Can the customer designate multiple witnesses for on-site destruction?
The customer may designate any number of witnesses for on-site destruction. The Certificate of Destruction names each witness by full name and signature, and the witness signs at intake and at completion. Data Destruction Inc accommodates customer-side compliance officers, internal-audit observers, and external auditors as designated witnesses.
How long must the Certificate of Destruction be retained?
Retention period follows the customer’s regulatory category. HIPAA documentation is retained 6 years from creation or last effective date per 45 CFR §164.530(j)(2). FACTA Disposal Rule documentation has no fixed federal retention; FTC enforcement actions cite multi-year retention as expectation. Defense (cleared) retention follows NISPOM and the contracting agency’s specific clause. The customer retains the CoD; the vendor retains a copy for the same period.
Should the Certificate of Destruction be issued before or after recycling-stream handoff?
The Certificate of Destruction is issued upon completion of destruction (the irreversibility moment), not after recycling-stream handoff. The CoD references the downstream recycling stream by certification (R2v3 or e-Stewards) and processor name; recycling-stream completion is a separate milestone documented in the recycling-stream paperwork.
Which Related Data Destruction Inc. Resources Cover Hard Drive Destruction Vendor Selection in Depth?
Procurement officers and CISOs evaluating hard drive destruction vendors typically pair this guide with Data Destruction Inc. compliance and service-mode references that cover NIST 800-88 method mapping, HIPAA disposal documentation, on-site witnessed shredding mechanics, and supply-chain ITAD vendor vetting. Each linked resource expands one decision-criterion in depth.
For the regulatory citations applied above, review Data Destruction Inc. HIPAA data destruction requirements and PCI DSS data destruction requirements, which break down the HIPAA Disposal Rule (45 CFR §164.310(d)(2)) and PCI DSS v4 Requirement 9.4 with the audit-evidence specifics Procurement should require in the RFP. For the editorial framework on vendor vetting beyond hard drive destruction, Data Destruction Inc. supply-chain data sanitization vendor vetting extends the 9 criteria to broader ITAD scope. For the operational mechanics of on-site mobile shredding (the witness-mode-1 path), see hard drive shredding and the underlying data destruction service overview. Procurement officers requiring on-site witnessed destruction with NAID AAA chain of custody can review certified hard drive destruction service for service-mode and pricing details.
